How to Apply an IT Security Policy on Your Macs
With cybercrime on the rise, it is becoming increasingly important to ensure you have a robust security policy applied to the Macs in your business.
With macOS devices, there are a large number of security settings that aren’t enabled by default on macOS, leaving “out of the box” devices in a more vulnerable state.
The good news is that business users can reduce the risk of potential data security headaches by implementing the right security policy on their Macs.
It’s an unfortunate fact that your own users are often the weakest link within the IT security chain, but the following tips will ensure your network of Macs is as safe, secure, and compliant as it should be – without sacrificing usability.
Decide which controls you want to put in place
The security controls you need for your Macs will be dictated by:
- your clients;
- your industry; or
- both (more likely).
Equally, there could be the controls that are specifically valuable to your business and the type of data or content you work with.
The best way to approach this is to research your industry’s recognised controls. Don’t invent your own! A quick chat with an expert from a team like the one you’ll find at moof IT will provide you with the best insight into what you need to do.
Security controls shouldn’t impact the user experience, either. This is why it’s important to discuss the potential impact of any controls you put in place and identify the best way to make them as seamless and inconspicuous as possible. Apply that same mindset to your customers because your Macs will play a key role in their journey, too.
Just remember to get everything written down, and when you reach out to the experts, make sure you go armed with as many questions as you need.
Agree your final policy
Having a Mac security policy is vital, whether you’re in the early stages of building an SME or running a large, established enterprise.
Yours will include a number of specific security controls, each of which you’ll have researched and identified as important during the first stage of this process.
The next step is to agree on the final security policy that’ll be applied to each of your Macs. This might include:
- firewall configurations;
- remote access;
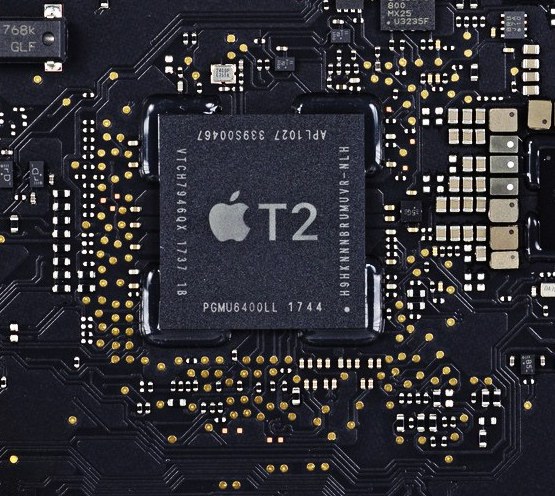
- file encryption;
- specific antivirus tools;
- disabled automatic logins and guest accounts;
- password management; and
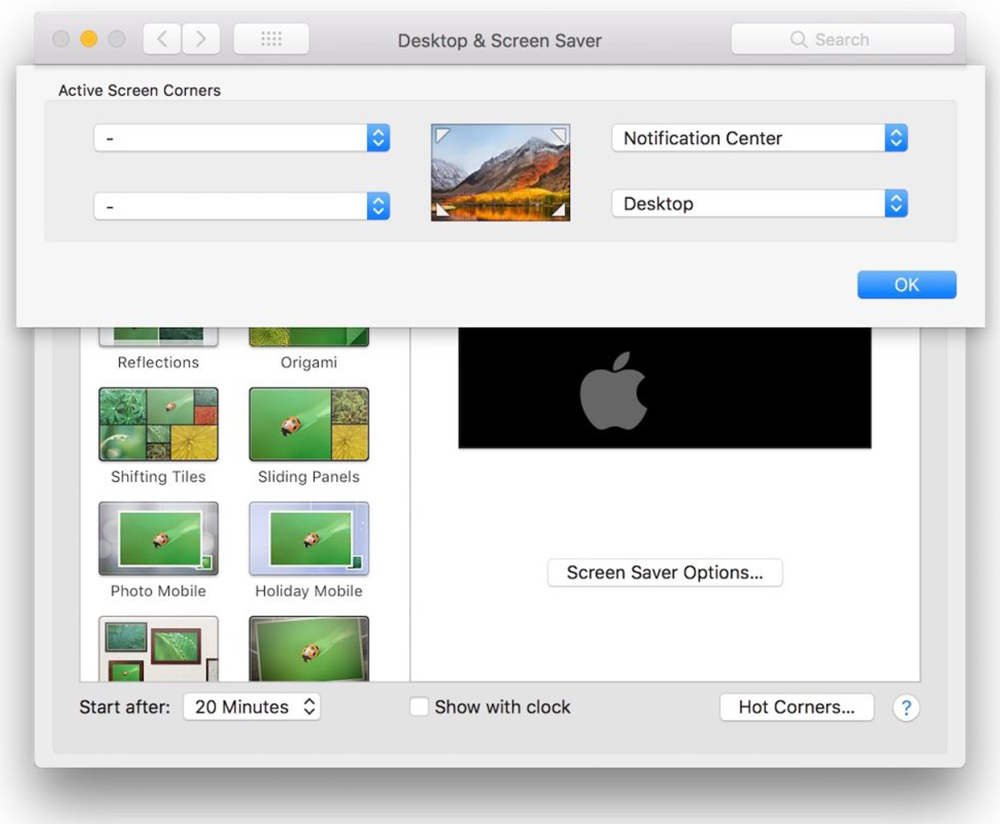
- a reduced feature set (for instance, no access to Spotlight suggestions).
Once you’ve agreed on the final list of controls, you’ll need to test each one. This is important because testing might reveal unwanted side effects on some of your Macs, causing issues with productivity or useability.
This will also help you check the compliance for each Mac against each control. Chances are, you’ll have a number of models, from MacBooks to iMacs, all from different eras and running various OS versions. They may not respond identically to your security policy and it’s vital you identify any potential issue early on.
Putting the policy into practice
Now, it’s time to deploy and enforce the security policy. This involves enabling the settings on each device and, in many cases, enforcing them to ensure that those devices cannot fall out of compliance.
This is where hiring a specialist is a smart idea. Someone who is Apple-focused and familiar with MDM solutions will be able to undertake all of the configuration and testing required to ensure that the polices are deployed correctly in the future and with limited effort on your part.
More importantly, they’ll make sure your security policies don’t impact on the user experience delivered by your Macs.
Monitor, monitor, monitor
Applying an IT security policy to a network of Macs isn’t a one-time job. You’ll need to monitor it constantly to ensure that no leaks or gaps appear.
Bad things happen, unfortunately. FileVault might fail to enable itself on a particular Mac; one device might inexplicably stop checking in; updates might fail to install.
Just as you need to keep a close eye on your backup services, IT security policies require a strict eye placed on them at all times.
No matter how much research you undertake initially, your IT security policy simply cannot be 100% robust in the real world when those Macs are put to use.
Make sure someone is tasked with monitoring the policies and put in place a process to respond to and remediate any compliance issues. Leveraging an inventory system like Jamf Pro, you can query the devices easily to spot any cases of non-compliance against your set of specific security controls.
If you need help and support with your IT security policies for Macs, just get in touch with the friendly Moof IT team.