Everything You Need to Know About Administrative Rights
When it comes to IT administrative rights, it can be difficult to decide on the best policy for your business. This article will explain what admin rights are, how they can affect users on a day-to-day basis, and why it is often more secure to limit their use. Hopefully this will help you in making an informed decision and understand what’s involved in removing admin rights, the next time this matter comes up.
What are administrative rights?
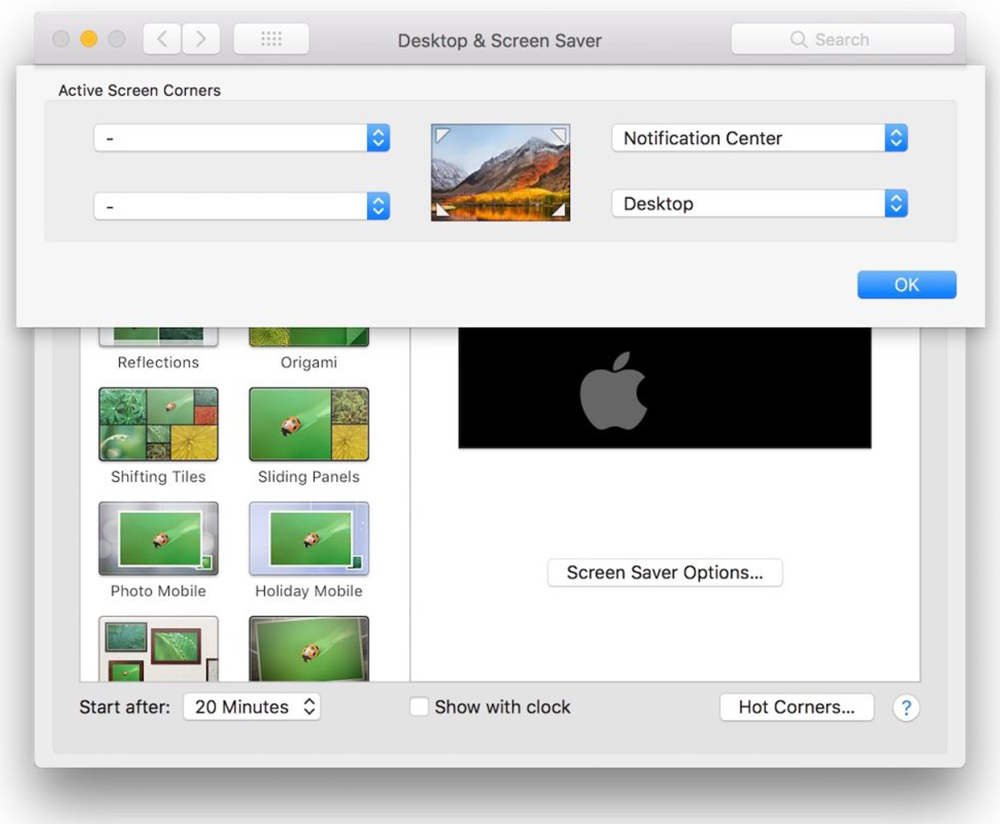
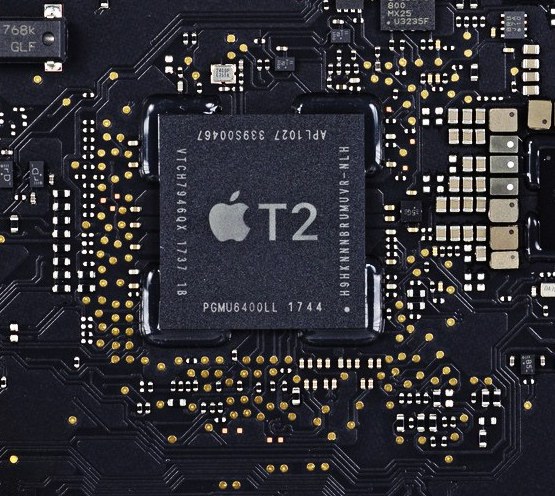
Admin rights, also known as user permissions, is the collective term for all authorisations given to users (company employees) in relation to their Macs. For example, administrative rights enable users to access network resources, like data files, printers and scanners, and to make modifications to applications when needed.
How do administrative rights reflect authority?
As administrative rights are a form of permission, they can be regarded as a reflection of authority within the business. There are also different levels of user permissions available on Macs. If, for instance, someone is listed as a standard user – which is the usually the case for most employees – they can often complete their day-to-day tasks without requiring administrative rights.
However, higher level permissions are most likely to be granted to more senior staff members and people within IT teams, so they can make informed decisions about computer software installation and modifications that require administrative rights.
Pros and cons
Having admin rights can save time. For example, if employees need to install a new piece of software, they won’t have to log a request with the Service Desk/IT team for approval if they are administrators on their machines.
However, granting administrative rights, particularly to all team members as a blanket option, can put your organisation at risk. Security and compliance issues can emerge quite easily when these rights are given to people without an understanding of what’s involved. Viruses or malware could end up being downloaded by accident because an employee installed what they thought was a legitimate software update, for example.
Users with full admin rights are also able to copy sensitive data, edit source code for software and install anything on the device. They could also end up deleting files that contain important business information, whether knowingly or accidentally. So, if you’re not sure who you’re giving these administrative rights to, then you’re taking a huge risk.
Whether you’re an enterprise, SME or educational organisation, it’s important to make sure that the administrative rights you’re granting your staff are appropriate for their role and responsibilities.
Taking away administrative rights: Is this more or less secure?
When it comes to Mac security, administrative rights play a key role. Whether or not you take away administrative rights from employees should depend partly upon whether they are needed for them to perform their specific role.
It is important to avoid giving everybody full administrative rights by default, as this could lead to someone without the necessary knowledge accidentally compromising IT security. For instance, installing an update which is actually a form of ransomware or removing basic security controls such as Filevault. That said, all users require the ability to make some changes to their devices to ensure their ability to work is not restricted which begs the question…
What is the right level of administrative rights for my employees?
The simple answer is this will vary depending on the type of work your users are doing, so the safest solution is to start with minimal permissions and build up as needed. The majority of users will be able to work perfectly well as Standard User and will not require admin rights but those in more technical roles such as developers may need them. In these cases, make sure users understand what these rights mean in terms of permissions, what to look for in files to avoid potential phishing scams, and what your company IT security policy is to ensure they do not breach it.
Are you unsure about implementing administrative rights for your business? Contact us today so a friendly and experienced member of our team can help you.